The Digital School Team at North Lanarkshire Council have shared this summary of their recent work using Minecraft with primary school learners. To find out more get in touch with Alan Cooper Curriculum Manager CooperAl@northlan.gov.uk and Lauren McIntyre Digital Education Support Officer McIntyreLa@northlan.gov.uk at North Lanarkshire Council
All resources and support are available on our Padlet below
North Lanarkshire Minecraft Build Battles
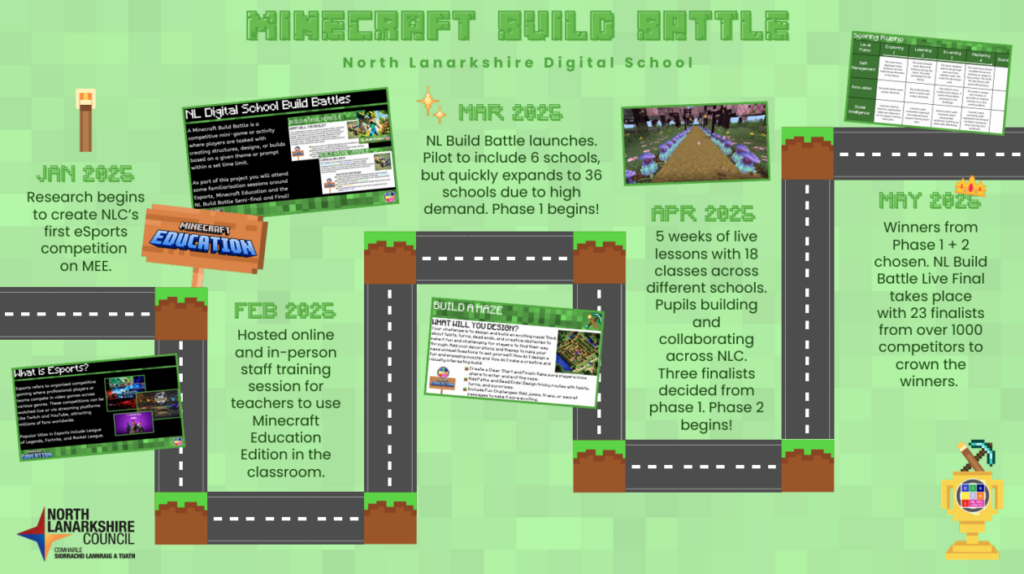
Roadmap of Journey
NL Minecraft Build Battle Summary
In Session 2024/25 North Lanarkshire’s Minecraft Build Battle was launched! Inspired by the rapid rise of esports across Scottish education, the final was the culmination of months of competitive gaming.
From February 2025, over 1000 pupils took part in live online lessons and in-class challenges led by North Lanarkshire’s Digital School Team. Pupils from 36 schools worked together in teams of four within their class to develop their collaboration and Minecraft skills. They completed builds each week based on prompts with increasing difficulty and relevant success criteria. Following an in-class build battle, teachers chose a winning team to represent their school in one of the live online semi-finals against five other teams. The top-performing six teams were then invited to showcase their creativity and skills at the inaugural in-person live build battle final!
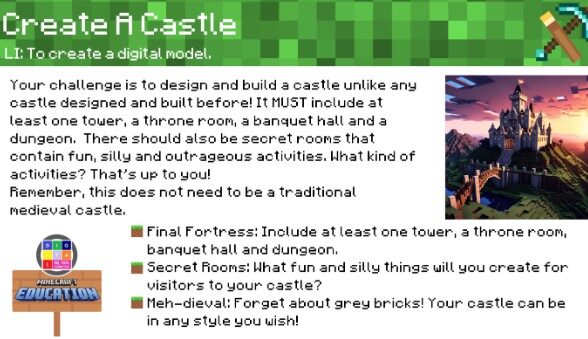
The 24 pupils from six teams were challenged to create a fantastic castle for the famous Minecraft character, Steve, within 45 minutes.
After lengthy discussion and deliberation, judges from North Lanarkshire Council and the eSports and Gaming industries decided the winners – ‘The Glowstone Gals’ from Thornlie Primary, Wishaw.
Build Battles by Number
- 37 schools (35 Primary & 2 ASN Primary)
- 36 in class build battles
- 6 live semi-final build battles (144 pupils)
- 1 live grand final (6 schools & 23 Pupils)
- Clusters (20 clusters involved)
Feedback by pupils and teachers include:
North Lanarkshire Council: Minecraft Battle Builds Live Final Video Long
Teacher
‘It was incredibly well organised and launched effectively, the CPD sessions were great for someone with zero experience of Minecraft. the build prompts were really good and I found FULL class engagement. I have a child in my class (P7) working at early level in all curricular areas and this is one thing they could join in with peers – very inclusive.’
Pupils
‘Our class really enjoyed it because we helped each other and our friendships grew’.
‘I really enjoyed Minecraft Education. It really helped to develop teamwork skills and creativity. It was mega fun and I really hope our teacher does this with the next P7s’.
‘The prompts were very creative because each week they were different but gave us a chance to add our own touches. I hadn’t played Minecraft in a while but not I’m constantly playing Minecraft Education with my friends!’
Plans are already underway for a Minecraft MAYhem event in this session. A focus on eSports in Primary and Secondary schools will also be a target for the NL Digital School.























You must be logged in to post a comment.